Authentication and Email: What It Is—and Why It Matters
Published on April 03, 2019/Last edited on April 03, 2019/5 min read

Lauren Leonardi
WriterWhen marketing, growth, and engagement teams talk about email, it’s often in the context of email engagement—are the marketing emails they’re sending working? What are recipients responding to and what are they giving the cold shoulder? But to even get to the point where you can send those email campaigns, there’s a bunch of boxes to check and technical hoops to jump through. IP pool setup, Figuring out subdomains. IP warming. And one of the least understood aspects of it all: email authentication.
Not entirely sure what we mean by email authentication? It’s okay. We’ll begin at the beginning and keep this as straightforward as possible. Because although the land of email authentication is filled with acronyms and complicated terms, it all basically boils down to internet service providers (ISPs) doing their due diligence to make sure that the people behind large email sends aren’t secretly phonies-phishers-scammers.
What is email authentication and why is it necessary?
Remember the days of yore (e.g. the late 1990s) when everyone received at least one email from a Nigerian prince who’d make us rich if only we’d wire him $1,000 “discreetly and intelligently at our earliest convenience”? Scam and spam emails are more subtle and crafty these days, and email more ubiquitous. So, ISPs have made it their business (literally) to safeguard the channels of communication by making it easier to be sure that the emails you receive are actually from the people who are listed as the sender. ISPs take the job of keeping spam out of their users’ inboxes very seriously—and they tend to take something of a guilty-until-proven-innocent approach. They’re attempting to tame the Wild West of email sending and receiving so that consumers like you and I only receive email we want to receive.
Through a process of proper authentication, ISPs can ensure that scammers don’t impersonate you and wreck your hard-earned reputation! (Remember: a bad email reputation means that the emails you DO send don’t reach as many people, even if they’d be completely psyched to get them.)
Email authentication exists for your safety as well as your customers’ safety—after all, you don’t want your brand’s identity corrupted any more than your customers want to receive emails from bad actors impersonating you.
How does authentication work?
Ultimately, authentication is about ensuring that the emails people receive were actually sent by the people or companies who are listed as the sender. However, there’s a hiccup that ISPs have to deal with: the Simple Mail Transfer Protocol (SMTP), which is the basic email sending protocol that makes email possible, doesn’t include a built-in authentication process. To address this issue, additional standards designed to support effective email authentication have sprung up. The big ones?
SPF
Not to be confused with sun protection, SPF in this case refers to Sender Policy Framework. You’re the sender here, so SPF simply means you (or any other sender) get to choose what IP addresses are allowed to send from a specific domain.
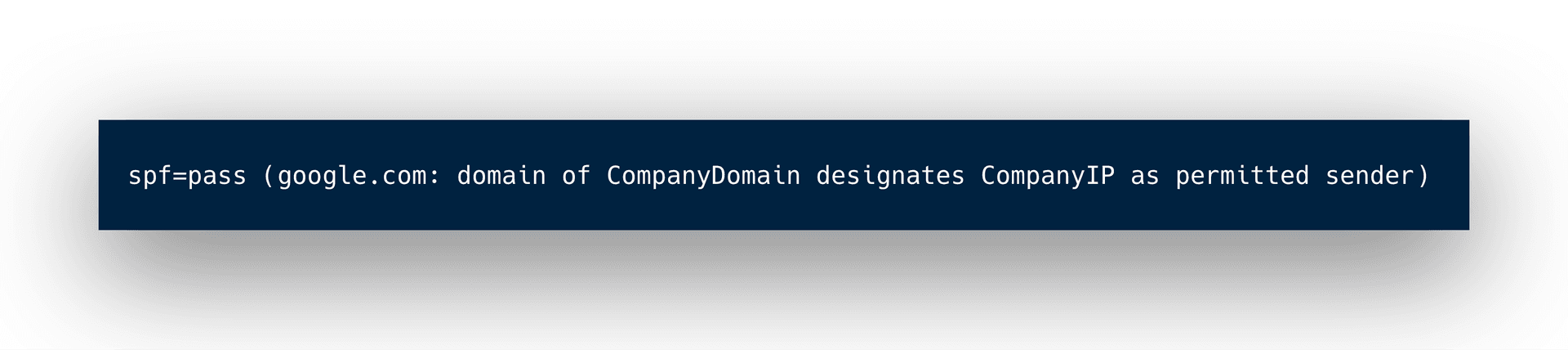
How does that help with authentication? Well, SPF makes it possible to suss out possible scammers by allowing mailbox providers to compare the IP address associated with an email against a list of authorized sending IP addresses that are published in the domain name system (DNS) records for the sender’s domain.
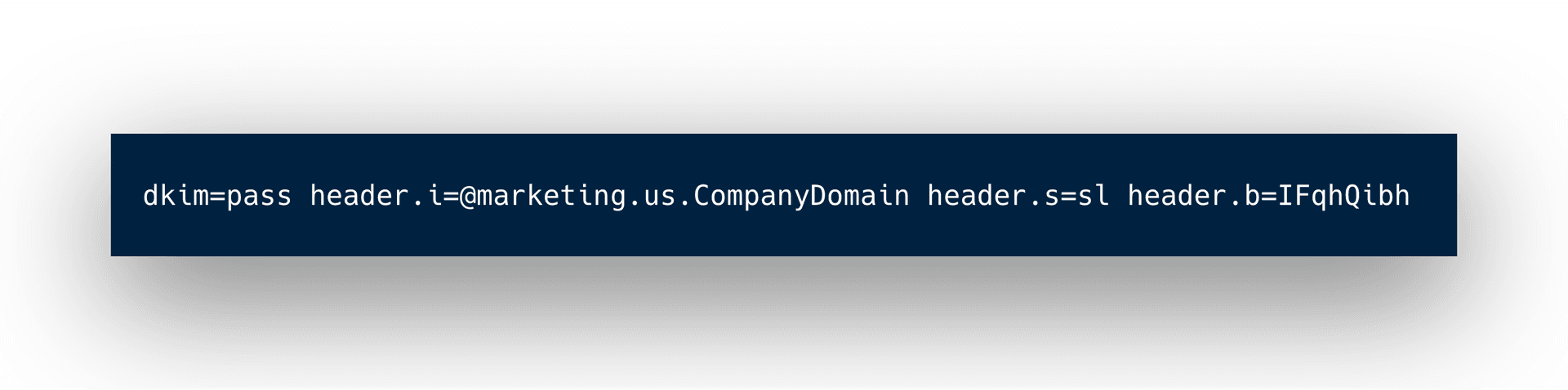
DKIM
The acronym stands for Domain Keys Identified Mail. DKIM provides an encryption key and digital signature with each message to make sure nothing was falsified in the creation or sending of an email. This process ensures that your emails arrive whole, with their full integrity, in the correct users’ inboxes, uninterrupted by cybercriminals.
DMARC
While both SPF and DKIM provide important safeguards, DMARC plays a key role by serving as a unifier that brings the benefits of both those standards together. DMARC stands for (ready?) Domain-based Message Authentication, Reporting, and Conformance.
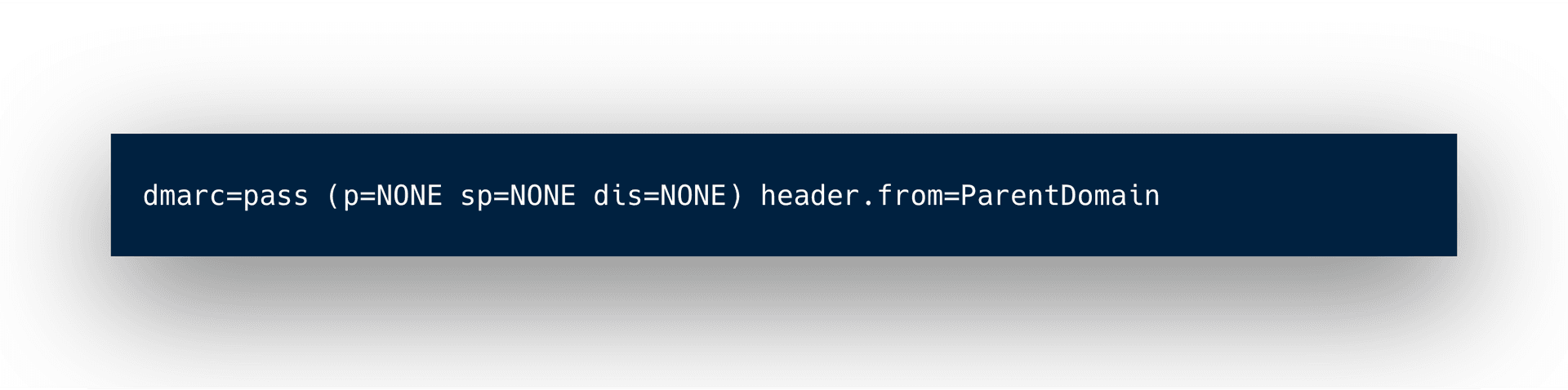
DMARC can be thought of as a communication stream or feedback loop between senders and mailbox providers. A mailbox provider will give a report to senders of what they are seeing, and senders give mailbox providers specific instructions on how to handle the message if it does not meet the required criteria (nothing, quarantine, reject). This combined process makes it more difficult for scammers to impersonate you. Plus, it empowers senders to have additional control post-send.
How much do marketing, growth, and engagement teams need to understand about email authentication?
If you work on the customer engagement side of your brand’s email program, you’re probably off the hook when it comes to knowing all of the specific ins-and-outs of how this works. That said, knowing what authentication is, how it works, and why it matters makes it easier to ensure that your email efforts aren’t being hamstrung by poor implementation in this area.
One key caveat: While both SPF and DKIM are relatively simple to set up and may be done by whatever ESP you’re using, DMARC implementation will likely require more of your team’s involvement. So if you’re going to take advantage of this standard as part of your email authentication efforts, make sure you study up here before getting to work.
When in doubt, keep it simple
All of the terms and stages of the process explained here are, in short, steps to ensure that your emails are sent from authorized servers, through legitimate means, to arrive safe and whole in your recipients’ inboxes. Good authentication bridges the gap between mailbox providers, email service providers, and marketers like you. The end goal is overall better ROI, and the path to better ROI in this case is solid deliverability and reputation. Don’t lose sleep over this process, but don’t shortchange it, either.
Want to dig deeper into sending great email and mastering deliverability? Check out “Emails on Email,” our interactive look at modern email marketing and where it’s going.
Related Tags
Be Absolutely Engaging.™
Sign up for regular updates from Braze.
Related Content
 Article6 min read
Article6 min readFrom Account Executive to Sales Manager: John Murphy on Building a Career at Braze
May 28, 2026 Article11 min read
Article11 min readExploring the technical side of ingesting data into Braze
May 28, 2026 Article10 min read
Article10 min readMarketing automation segmentation: How to create hyper-targeted campaigns
May 28, 2026